Explaining DDoS Attack and how to protect your site from it
 By Admin
By Admin

Nowadays, websites and online platforms are increasingly becoming targets of cyber attacks and a Distributed Denial of Service (DDoS) attack is one of the most widespread and destructive forms of cyber attacks. DDoS attacks are designed to flood a website's servers with a flood of fake traffic, making the website inaccessible to its users. In this article, we'll dive into DDoS attacks, the impact they can have on a website, and most importantly, measures you can take to protect your WordPress site from DDoS attacks.
From understanding the basics of DDoS attacks, to implementing security measures and best practices for keeping a DDoS-safe website, this article will provide a comprehensive guide to protecting your site. What are DDos attacks? DDoS is known as a denial of service attack, which is a type of electronic attack that aims to disrupt the normal course of operation of the target party's server, services, or network. Attackers use a large number of compromised computers and devices, also known as botnets, to send a large number of requests to the targeted server.
The main goal of these types of attacks is to make a website or service unavailable to its users, by flooding the server with a flood of requests. The attack achieves its goal after making the server unable to respond to user requests, which ultimately leads to the service crashing or being temporarily unavailable. How DDoS Attacks Work DDoS attacks involve using a large number of compromised devices to overwhelm a server at the same time. The attacking device creates a botnet known as “botnets” by infecting many computers from different parts of the world with malware and controlling them as a group without the knowledge of the owners.
The attacking device forms the control unit that sends commands to the attacked devices on a specific day and time, and at the planned time, the attack on the targeted server begins from all devices at the same time. Which constitutes confusion and disruption to the server’s workflow, consumption and damage to server resources such as the central processing unit and memory, in addition to consuming network bandwidth, which results in the computer connected to the targeted server facing a block of services, as the massive influx of DDoS attack will prevent the server from responding to its requests. The first DDoS attacks were reported in 1999. The attacks continued and mainly targeted prominent websites including Yahoo, Amazon, and eBay.
As technology advances, attackers begin to use botnets and networks of compromised devices to launch more powerful attacks. With the advent of the Internet of Things (IoT), the number of devices that can be compromised and used in DDoS attacks has increased dramatically. Nowadays, DDoS attacks are becoming more frequent and powerful.
Read also: What are DDoS attacks? How do you protect your WordPress site from them?
How attacks affect targeted sites may be
The reason behind DDoS attacks is financial. Competition pushes some companies to launch DDoS attacks against their competitors to disrupt their business, steal their customers, or dominate the market, which may cause the targeted party to reduce their brand reputation and harm their business profits. It may be a type of protest against policies or beliefs, aiming to disrupt the operations of the targeted organization. Attacks may be launched just for fun as a form of challenge or to showcase their skills by exposing the vulnerabilities of a targeted website or network.
A DDoS attack can have a significant impact on a targeted website. When a website is attacked: its user may not be able to access it, which makes it impossible for them to access the information or services they need, affecting your reputation as a website owner and your position in search engines. DDoS attacks can consume large amounts of network bandwidth, causing the website hosting provider to incur additional costs.
If the website hosting providers are unable to handle the attack, the website may be taken offline for an extended period of time. DDoS attacks can also cause other security risks such as data breaches or other types of cyber attacks that can exploit vulnerabilities created by DDoS. The effects of a DDoS attack on websites can be devastating, and it is important that websites take the necessary steps to protect themselves from these types of attacks.
How to protect your site from DDoS attacks To protect your WordPress site from DDoS attacks, it is important to understand the common symptoms of an attack. This can include sudden spikes in site visits, slow loading times, and difficulty accessing the site. To monitor your website's visits and resources, you can use tools such as Google Analytics, server logs, and network monitoring software.
By identifying the signs of a DDoS attack early, you can take steps to protect your website and reduce the impact of the attack. Implementing Security Measures Taking security measures is an important step in protecting your WordPress site from DDoS attacks. Here are some examples of security measures you can take and steps to implement them: Use a Web Application Firewall (WAF) Installing a WordPress firewall makes your site more secure and less vulnerable to hacking.
The firewall forms a barrier that prevents vandals from accessing the site, and prevents bypassing its protection measures. WAF (Web Application Firewall) is a security tool that helps protect a website from various threats such as DDoS attacks. It works by monitoring and analyzing incoming traffic and blocking anything that matches a set of pre-defined criteria, helping to prevent the server from being overwhelmed with traffic.
There are several WAF plugins for WordPress that can help protect WordPress sites from DDoS attacks by providing a firewall to limit the number of users accessing your website during a specific period, IP blocking to block known attackers, the ability to filter out potentially bot visitors, malware scanning, and regular updates. The most famous of them are: Sucuri Security, Wordfence, Jetpack. It is important to choose a plugin that is updated regularly and is known for its effectiveness among users.
Read more about the 5 best plugins to secure and protect your WordPress site with all security features to learn about examples of plugins that you can use to protect your site, their characteristics, advantages and disadvantages, as the choice of plugin depends on your specific needs and the features you are looking for. Read more: A comprehensive guide to the Web Application Firewall (WAF) Use a content delivery network (CDN) Subscribing to CDN services guarantees the complete safety of your site data on the hosting site in the event of any malfunction or hacking of your site. Its services include providing copies of your website on data centers distributed around the world, so that a copy of your site is displayed to visitors from the data center closest to them, which reduces the pressure of visitors or potential attacks on the primary server.
A CDN helps prevent DDoS attacks by: Delivering saved copies of your site Reducing stress on your servers Reducing load times Detecting and mitigating strange traffic patterns A CDN improves overall website performance and effectiveness, and integrates easily with WordPress. Cloudflare is one of the most popular service providers and offers free and paid plans, which vary according to the features it offers in each plan. Read also: An explanation of CDN services and how they work to increase the speed of your site. To learn about the advantages of content delivery networks and their most famous service providers.
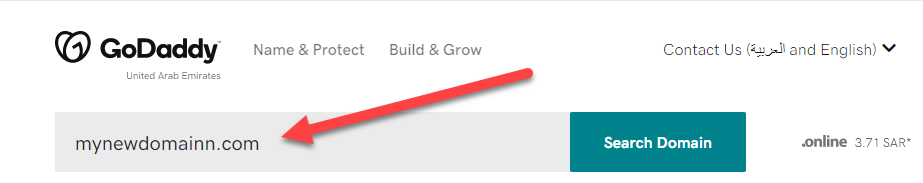
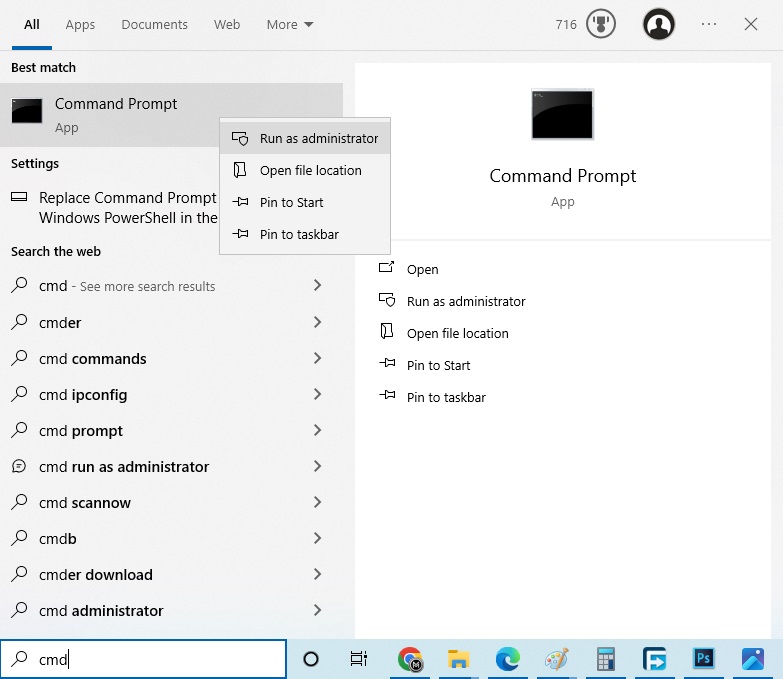
Disable XML RPC Disabling XML-RPC in Woodpress can be an effective way to protect your website from DDoS attacks. XML-RPC is a feature that allows third-party applications to interact with your WordPress website, but if you do not use a mobile app or third-party applications to manage your website, you can disable XML-RPC to reduce the possibility of an attack on your website. Here is a simple way to disable XML-RPC in WordPress. If you do not have technical experience, it is a good idea to consult the developer before disabling it: 1. Locate the htaccess file from the site files.
2. Open the .htaccess file in a text editor. 3.
Add the following code to the file: order deny,allow deny from all 4.
htaccess file and upload it to your server. This will block all requests to the xmlrpc.php file, effectively disabling XML-RPC on your website. Read also: Disabling access to the XML-RPC file within a WordPress site Best practices for keeping a WordPress site protected Here are additional tips for securing a WordPress site from DDoS attacks: 1.
Use Secure Hosting Good hosting provides the infrastructure and tools needed to protect your website from DDoS attacks. It may provide you with increased security levels such as instant operating system updates, a robust server-level firewall installation, built-in DDoS protection, and access to specialized DDoS protection services. Read more: The best reliable hosting company Read more: The best WordPress hosting 2.
Make continuous updates Websites that use older versions of WordPress are more likely to be hacked. Regular updates to your website, themes, and plugins not only add additional features, but may also come with solutions to problems and fix security vulnerabilities. Read also: How to get WordPress updates automatically. Using templates and plugins from trusted sources is an important step to protect against DDoS attacks.
Trusted sources like the official WordPress account go through a review process to ensure that the themes and plugins they offer are safe and free of vulnerabilities. 3. Login Page Protection Login protection is a way to protect your site's login page against hacking and phishing attacks.
1. Use a strong password and a unique username: It makes guessing attacks on the site more difficult and increases the security of the site. 2. Enable Two-Factor Authentication (2FA): Used to distinguish site users by requiring them to provide their login data and a second identification requirement, such as an alphanumeric code sent via SMS, email, or phone call.
Read also: Increase the degree of security of your WordPress site with the Google Authenticator application 3. Add a CAPTCHA to the login page: to ensure that anyone trying to log in to the site is a real human. Read also: Change the link to the WordPress login page and activate reCAPTCHA 4.
Limit the number of login attempts and set a time for the login page to expire: that is, users who repeatedly enter incorrect login data will be blocked and prevented from accessing the site after a certain number of attempts. The person must refresh the page and start the login process again after the expiration time has passed. Read also: Secure and protect WordPress sites from all vulnerabilities 4.
Back up your site regularly Backing up your site regularly is an important step in protecting it from DDoS attacks. DDoS attacks can cause significant damage to your website, including data loss and disruption of service. By creating regular backups of your site, you can ensure that you will be able to restore it to its previous state in the event of an attack.
This can help reduce downtime and reduce the impact of an attack on your business. Read also: Ways to backup WordPress sites for free to learn about the best free ways to back up your site. Read also: An explanation of making a backup copy of your site to secure it from any damage. In conclusion, DDoS attacks are a malicious attempt to disrupt the normal traffic path of a targeted server, service, or network by flooding the target or the infrastructure surrounding it.
The effects of DDoS attacks can be severe, causing a website to become unavailable to users, resulting in lost revenue, and damaging the reputation of the targeted organization. So to protect your WordPress site from DDoS attacks, it is important to understand how these attacks work and the different methods that can be used to defend against them. To obtain strong protection, you must use a group of different methods, and using one of them is not enough to guarantee the highest level of security possible.
DROPIDEA
We hope this article has added real value to you. At DROPIDEA, we always strive to deliver high-quality content that helps you grow and evolve in the digital space. Follow us for more useful articles and guides.

Admin
DROPIDEA
Latest Articles
“Nofollow” tag: What it is, how and where it is used, “Infographics”

ASUS ROG Flow Z13 (2025) available: Everything you could dream of in a gaming tablet.

The best 5 sites to download safe computer programs without malware!

Create a forum on WordPress using the bbPress plugin step by step

New data reveals how much brands pay influencers
Related Articles

ASUS ROG Flow Z13 (2025) available: Everything you could dream of in a gaming tablet.
Pay attention: 10 symptoms that confirm damage to the hard disk and the need for your quick intervention!